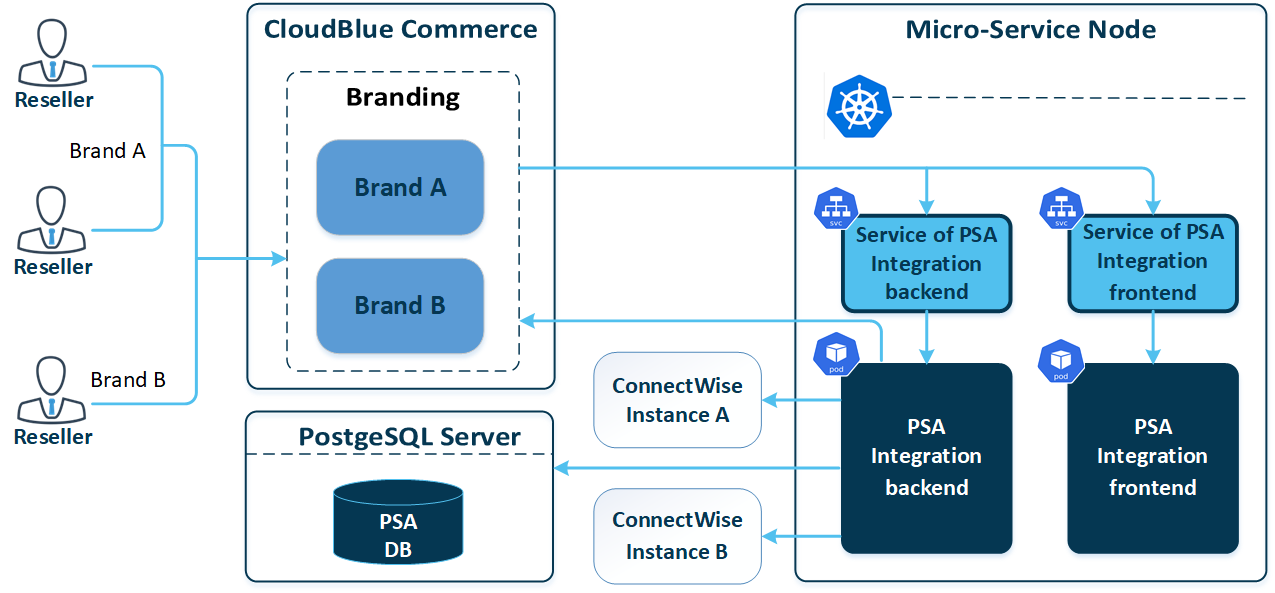
High-Level Architecture
PSA Integration is a microservice that is deployed as a Helm release in a Kubernetes cluster with its own release cycle. It is not included in the CloudBlue Commerce distribution package by default and must be installed to the platform separately. One PSA integration instance serves all resellers on a CloudBlue Commerce instance.
The PSA Integration service consists of these three components:
- The PSA Integration frontend that serves static content (scripts, images, and so on) and is hosted in a separate container on the service node with installed Kubernetes.
- The PSA Integration backend that processes business logic requests from the frontend and is hosted in a separate container on the service node with installed Kubernetes.
- The PSA Integration database that is hosted on any DB node and provided as a service.
Installation Prerequisites
Before installing the PSA Integration component, ensure that:
- CloudBlue Commerce version 20.4 or later is installed
- A service node with a Kubernetes cluster is configured and registered in the CloudBlue Commerce platform.
- The PSA Integration database is prepared.
Network Requirements
The following ports must be open:
| From | To | Protocol | Port | Purpose |
|---|---|---|---|---|
| Browser | CloudBlue Commerce brand | HTTPS | 443 | To display content in a user browser. |
| CloudBlue Commerce brand | Service of PSA Integration frontend | HTTP | 80 |
To transfer static content (front-end scripts, images, and so on) to a user's browser. |
| CloudBlue Commerce brand | Service of PSA Integration backend | HTTP | 8080 | Transferring JSON data generated by business logic. |
| Service of PSA Integration backend | PSA Integration back-end pod | HTTP | 8080 | To pass internal K8s communication connections from the CloudBlue Commerce brand to the pod. |
| Service of PSA Integration frontend | PSA Integration front-end pod | HTTP | 80 | To pass internal K8s communication connections from the CloudBlue Commerce brand to the pod. |
| PSA Integration back-end pod | ConnectWise Management API | HTTPS | 443 | To transfer required ConnectWise data: product and customer identifiers, and so on. |
| PSA Integration back-end pod | PostgreSQL server | HTTPS | 443 | To store tasks, mappings and other PSA Integration-related entities. |
| PSA Integration back-end pod | CloudBlue Commerce brand | HTTPS | 443 | To transfer CloudBlue Commerce data related to orders and subscriptions. |
Resource Requirements
PSA Integration consists of a back-end pod and a front-end pod. The minimum Kubernetes resources required for the microservice deployment, including on-premise Kubernetes cluster deployment, are as follows:
-
Back-end pod
requests: cpu: 1000m memory: 768Mi limits: cpu: 4000m memory: {{ .Values.resources.limits.memory }}Note: The memory limit is configurable. The default value is 1280Mi.
-
Front-end pod
requests: cpu: 100m memory: 512Mi limits: cpu: 250m memory: 768M
Identity Service Requirements
PSA authenticates through Identity Service. Identity Service is required for each brand through which resellers access PSA. For information on how to create a Keycloak client for PSA, refer to Identity Service Management.
CloudBlue Commerce Brand Requirements
Resellers use their CloudBlue Commerce brands to access PSA. The PSA URL has the following format: https://${brand-domain}/${psa-url-suffix} (for example, https://cp.us.na.cloud.im/us-psa).
For each brand through which resellers access PSA, you must create rewrite rules:
- Download the
psa-brand-rules-ctl.pyscript to the management node. -
Add rewrite rules to the selected brand:
# python psa-brand-rules-ctl.py add ${brand-id} [--psa_url_suffix ${psa-url-suffix}]where:
${brand-id}: the internal ID of the brand through which resellers access to PSA.${psa-url-suffix}: (optional) the PSA URL suffix. If you set this parameter, PSA will be available at the following address https://${brand-domain}/${psa-url-suffix} instead of https://${brand-domain}/psa. Refer to Log-in URLs.
APS API Access Requirements
A precreated L0 staff member with OAuth credentials must exist in the system. This staff member must have the following GET permissions for APS types:
http://www.odin.com/billing/order-managementhttp://www.odin.com/billing/Subscription"http://www.parallels.com/products/automation/billing"
This staff member must have this POST permission for an APS type:
"http://www.parallels.com/pa/pa-core-services"
These permissions are configured in the System > Users > staff_member > APS Bus Access tab.